TegraRcmSmash
A reimplementation of fusee-launcher in C++ for Windows platforms.
Lets you launch fusee/shofEL2 payloads to a USB connected Switch in RCM mode.
Downloads
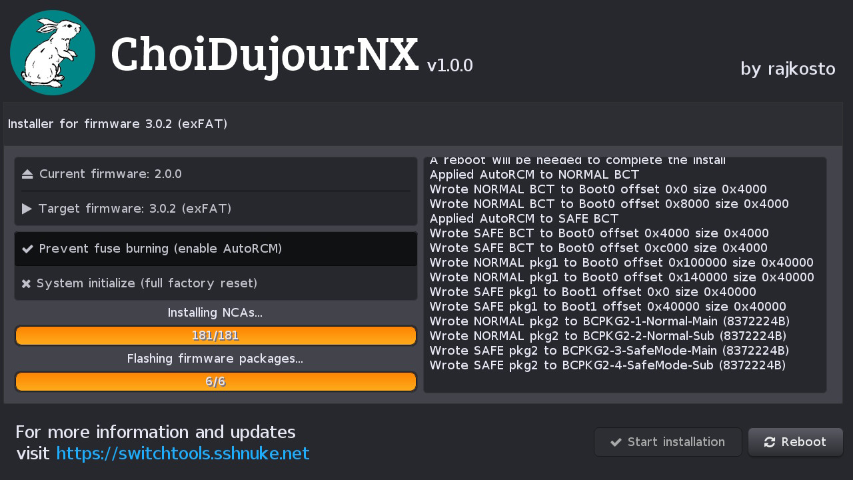
ChoiDujourNX
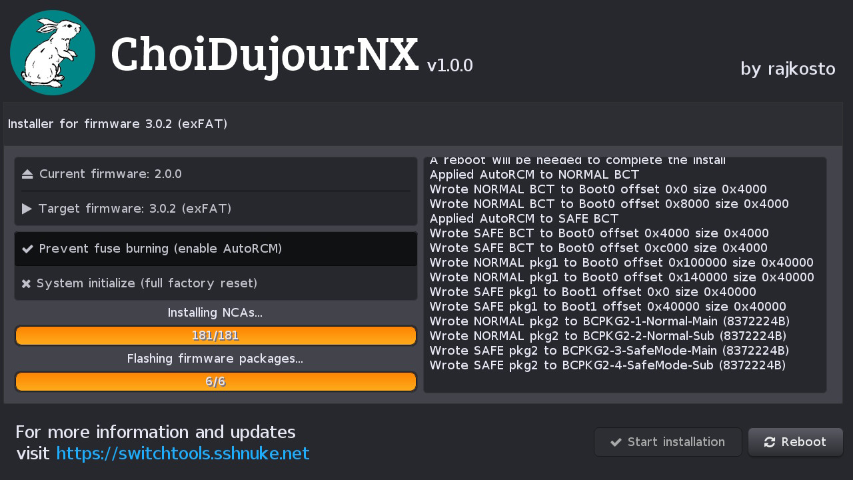
Homebrew for installing Nintendo Switch firmware update packages directly on the console, without burning fuses!
ChoiDujour
Converts Nintendo Switch firmware update packages to installable images/files that can be transferred to the device itself
- 1.1.0 (21.07.2018) ChoiDujour110.zip - Lets you choose what patches to apply to generated FS.kip1 via --fspatches parameter (try nocmac,nogc,nosigchk)
- 1.0.2 (16.06.2018) ChoiDujour102.zip - Prefer placehld content over registered if both are present
- 1.0.1 (16.06.2018) ChoiDujour101.zip - Fix critical bug where folder attributes weren't set
- 1.0.0 (15.06.2018) ChoiDujour100.zip - Initial release
RajNX (Deprecated)
Files only kept here for archival purposes, please use Atmosphere instead (or any repack that contains it)
- 0.7.5.1a(01.11.2018) RajNXv0751a.zip - Add SUCCulent ES patches for 6.1.0
- 0.7.5.1 (19.09.2018) RajNXv0751.zip - Support for officially released firmware 6.0.0-5.0
- 0.7.5 (18.09.2018) RajNXv075.zip - Support for firmware 6.0.0-4.0, additional nosigchk patch added
- 0.7.4 (17.08.2018) RajNXv074.zip - hbloader no longer stored in titles dir/010000000000100D, now it is in RajNX folder
- 0.7.3 (14.08.2018) RajNXv073.zip - Add PM, update creport, 1.0.0 launch profile is now Debug (for all firmwares), remove Tinfoil
- 0.7.2 (05.08.2018) RajNXv072.zip - Fully customizable hbmenu loader (you can choose the titleId and buttons required or not!)
- 0.7.1 (05.08.2018) RajNXv071.zip - Improve nogc (PreventGCUpdate) patch so it no longer has 10s hang on bootup and wakeup
- 0.7.0 (04.08.2018) RajNXv070.zip - Use own ini filename, logos, forks of bootloader and sysmodules, stop eclct from loading
- 0.6.9.1 (04.08.2018) RajNXv0691.zip - Update Tinfoil to commit 3a8d2c3 (fixes freezes)
- 0.6.9 (04.08.2018) RajNXv069.zip - Initial release
gptrestore
Restores the original Nintendo Switch GPT to your eMMC if you somehow messed it up ;)
briccmii
Corrupts (or fixes) the first byte of every BCT's pubkey in BOOT0 so your Nintendo Switch always enters RCM mode (or boots normally)
- v2 (19.06.2018) briccmiiv2.zip - Also checks (and restores, if requested) the correct keyblob into BCT
- v1 (21.05.2018) briccmiiv1.zip - Initial release
memloader
Parses ini files from microsd root and loads/decompresses/boots the appropriate binaries on the AArch64 CPU of the Nintendo Switch.
Ini files can be generated from source images using the programs inside tools subdirectory. Currently the tools understand coreboot CBFS images or ELF payloads (like u-boot).
- v3 (01.12.2018) memloaderv3.zip - Invoke Minerva memory trainer before starting selected binary, configurable via ini, improves performance of UMS by 80% !
- v2 (07.08.2018) memloaderv2.zip - Support additional boot ini parameters, change sample u-boot so that the ums mode works even if the partition table is corrupt
- v1 (12.05.2018) memloaderv1.zip - Initial release (contains precompiled u-boot ums modes as sample and the ini tools)
romdump
Dumps the RAW FUSE, KFUSE and BOOTROM bytes to your microSD/HOST PC via USB/console screen
biskeydump
Dumps all your Switch BIS keys for eMMC contents decryption, to be used as a fusee payload.
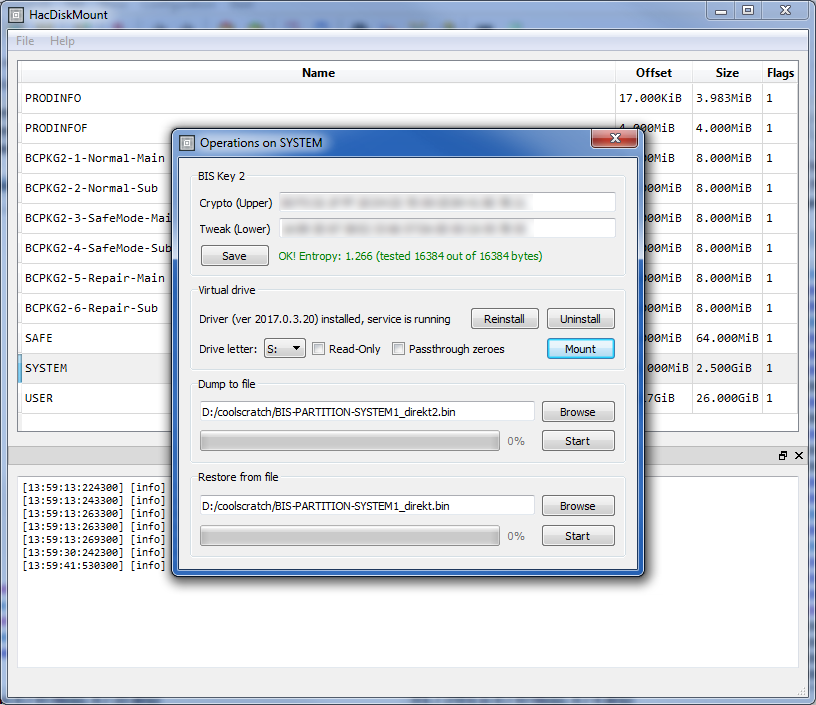
With all your BIS keys and your RawNand.bin (or the physical eMMC attached via microSD reader or using a mass storage gadget mode in u-boot/linux) you can explore/modify your eMMC partitions using my HacDiskMount tool below
Downloads
- v9 (22.06.2019) biskeydumpv9.zip - Support new tsec fw in 8.1.0
- v8 (05.02.2019) biskeydumpv8.zip - Support new tsec fw in 7.0.0
- v7 (27.11.2018) biskeydumpv7.zip - Support new tsec fw in 6.2.0 and add option to save keys to microSD
- v6 (04.05.2018) biskeydumpv6.zip - Outputs dumped keys text to RCM host if it's listening
- v5 (01.05.2018) biskeydumpv5.zip - Validate retrieved keys by reading a keyblob and verifying its MAC
- v4 (29.04.2018) biskeydumpv4.zip - First compiled release (v4 and up get TSEC FW from eMMC boot0)
HacDiskMount
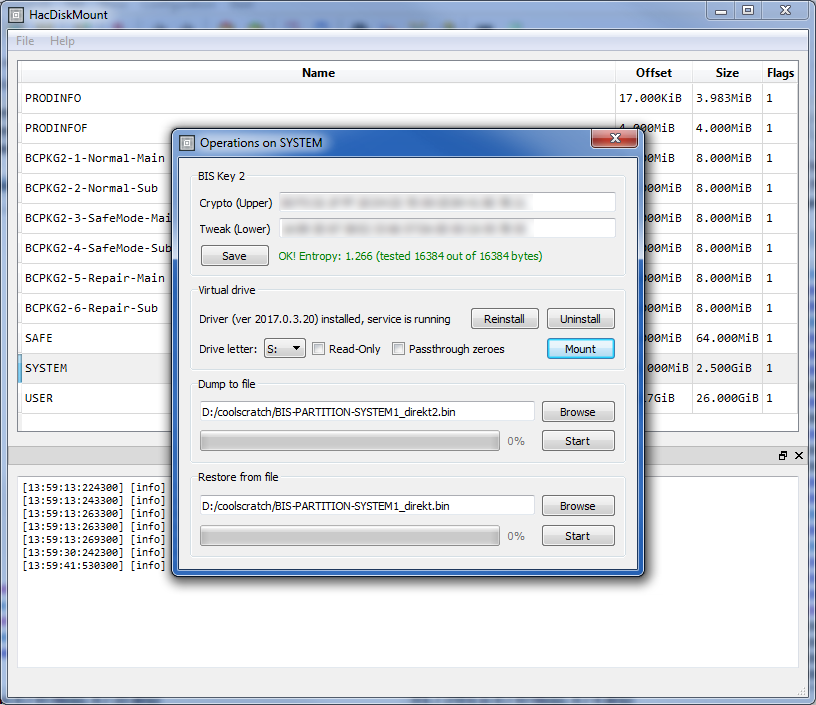
Allows to open Switch eMMC RawNand dumps (and physical devices) and lets you perform operations on the individual partitions within, such as dump/restore from file, or mount them as a drive letter in Windows (with transparent crypto performed provided you have your BIS keys).
Running all programs from this page requires that you have the Visual C++ 2017 x64 Redistributable installed.
Downloads
- 1.0.5-5 (27.07.2018) HacDiskMount1055.zip - Fix crash during crypto on pre-Nehalem CPU
- 1.0.4-4 (10.06.2018) HacDiskMount1044.zip - Improve performance of dump/restore partition operations
- 1.0.3-3 (29.05.2018) HacDiskMount1033.zip - Fix crash in open physical disk if there's a removable drive with no media
- 1.0.2-2 (30.04.2018) HacDiskMount1022.zip - Fix crypto not working correctly at all on CPUs without AES-NI
- 1.0.1-1 (30.04.2018) HacDiskMount1011.zip - Partial support for dumps on 4K physical sector drives
- 1.0.0-0 (25.04.2018) HacDiskMount1000.zip - Initial release
PartialAesKeyCrack
Multithreaded CPU-based (AES-NI accelerated, if possible) cracker for the "Partial Key overwrite" vulnerability in Switch secure-engine